Rocket Software Insights Hub
All results
Artificial Intelligence (AI)
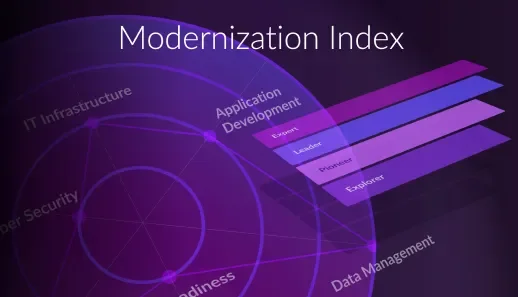
Assess Your Organization’s IT Modernization Maturity
Your personalized score shows where you are in that journey — and how to move ahead.
IT Modernization
Welcome to Modernization. Without Disruption.
We meet you wherever you are and tailor our strategies to align with your specific goals and objectives.
Application Modernization
Managing Technical Debt in Mission-Critical Environments
The arrival of the 2026 Gartner® Magic Quadrant™ for Technical Debt Management Tools points to increasing market awareness
Application Modernization
Rocket Software Recognized as Challenger in the 2026 Gartner® Magic Quadrant™ [...]
At Rocket Software, we’ve observed that the problem with technical debt is that it’s hidden until it’s not. That’s why we deliver comprehensive technical [...]
Data
Rocket Software Wins 2026 Award for Most Innovative Data Lineage Solution
Rocket Software has been named the Most Innovative Data Lineage Solution winner at the 2026 Data Management Insight A-Team Innovation Awards.
Security & Compliance
Rocket Secure Host Access UI: 2025-2026 Interface Updates
Modern Rocket Secure Host Access interface updates in 2025 and 2026 improve usability, IAM setup, audit reporting, compliance tracking, and secure host [...]
Hybrid Cloud
A Platform-Smart Approach to Mainframe Modernization
Evaluate workload placement across mainframe, cloud, and distributed environments in large estates with this Gartner® modernization research. Read more.
Data Integration
Rocket® Data Intelligence Recognized for Advancing Data Lineage
Named “Most Innovative Data Lineage Solution,” 2026 Data Management Insight A Team Innovation Awards
Security & Compliance
Getting Started With Rocket Secure Host Access: From Install to Live Session
Learn how to get started with Rocket Secure Host access and learn more about deployment, integration with existing IAM, and how to launch your first live [...]